We talk a lot about computer security and data security here at Lifehacker, but you can never have too many reminders of the basics. Here, in a nutshell, are the security tips and habits every computer user should know. Consider it a quick way to audit your own security.
Illustration by Fruzsina Kuhári. Photos by Jaymis Loveday, konmesa (Shutterstock) and Toria (Shutterstock).
10. Watch Out for Social Engineering Attacks

Let’s start off with perhaps the biggest security concern: Social engineering. It’s how hackers and data thieves cleverly access your secure information through phishing, impersonating other companies and people, and other common tactics.
Be suspicious of all links, emails, phone calls and other communications, but also know that most data breaches come from internal sources. You might be surprised at how easily even security experts can be fooled or hacked, so awareness is key.
9. Make Your Phone’s Lock Code More Secure

The default four-digit PIN for iOS isn’t the most secure. Head to the Settings app to add even just one more digit and your phone will be much more secure. The same holds true for Android: Longer is better.
There are also Android lock screen tools to boost your phone’s security. At the very least, consider changing your PIN if it’s one of these.
8. Back Up Your Computer Automatically

If you don’t make regular, duplicate backups, all the data that’s important to you isn’t secure. It’s not as much of a pain as you might think, so there’s no excuse not to back up your files.
We’ve shown you how to set up a backup system with CrashPlan, but you can also use Windows’ built-in tools or Mac’s Time Machine. (Heck, go nuts and build a Time Machine backup server with a Raspberry Pi.)
7. Install the Best Antivirus and Anti-Malware Software

Viruses and malware are always a threat. We recommend using one antivirus tool, such as Avira for Windows or Sophos Anti-Virus for Mac, as well as an anti-malware tool for on-demand scanning, such as Malwarebytes. Easy peasy.
6. Lock Down Your Wireless Router

Your router is the first line of defence for your home network. You know you should change the router’s administrator login, use WPA2 (AES) encryption and change other basic settings.
There are also some other Wi-Fi router security settings you might need to change right now. Think someone might have been stealing your Wi-Fi? Here’s how to find out and how to see everything that’s happening on your network.
If you want to share your Wi-Fi with friends, you can still do that safely.
5. Never Send Sensitive Information Over Email Unless It’s Encrypted
Sensitive information, such as your bank info, tax file number, tax returns or confidential business info, should never be sent over email without encryption. It’s too risky. Encrypt files with one of these tools before sending them or use a service like super simple ProtonMail or encrypt your emails with PGP. Encrypt all the things.
4. Don’t Use Public Wi-Fi Without a VPN
Yes, you really do need to worry about security when using public Wi-Fi. At the very least, it’s better to be safe than sorry. Here’s how to stay safe on public Wi-Fi networks.
Your best defence will be to use a VPN, or virtual private network. It keeps you safe even in other situations too. If you’re using a VPN to stay anonymous, that won’t protect you if you’re careless with your identity, but, aside from that, everyone can use a good VPN. Here’s a massive comparison spreadsheet to help you find the right VPN.
3. Use a Password Manager
Clever password tricks aren’t fooling anyone and because you should be using unique passwords for each site and service you use, it’s impossible to remember every password. That’s where password managers come in. We compared the best password managers here, but also took a look at which password manager is the most secure. You always have to weigh security and convenience, though, so just pick one that has the features you need.
2. Use Two-Factor Authentication
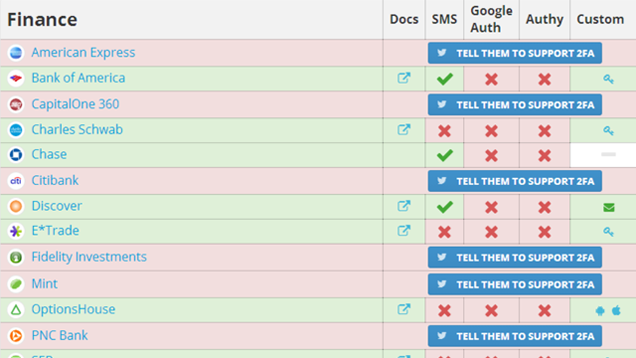
Please turn it on. Two-factor authentication offers the extra layer of security that protects you in case your password gets stolen. Use TwoFactorAuth to find out all the places you can turn two-factor authentication on.
And, don’t worry, if you lose your phone (most often used as the authentication device), you can still get back into your account if you plan ahead.
1. Regularly Review Your App Permissions and Security Settings

Finally, it’s not enough to just have all of the above set up, you have to still be vigilant and make sure your software is always up-to-date. We often forget about stuff like updating the router firmware or cleaning up our app permissions. Make this all part of your spring cleaning or perhaps a regular habit.
Here’s how to clean up your Facebook app permissions, clean out your Twitter app permissions, or use a site like MyPermissions to clean up multiple services, including Google and Facebook.
Google sometimes offers free storage just for doing a security check, so you can even get a bonus for keeping up with your security needs.

Comments
3 responses to “Top 10 Tech Security Basics Every Person Should Follow”
The thing about 2FA, is that the times that I most want it (overseas travel), is when it’s least useful (since I won’t necessarily have my phone with me). Sure some of them allow me to print out one-time-code pads, but then I have to limit myself to the number of logins I’ve printed, and then I need to make sure to carry the pad with me.
Or you get a local SIM to avoid astronomical phone bills.
I’m looking into dual SIM phones for this very reason. Make calls with the overseas SIM, while still receiving SMS messages with validation codes.
Why on Earth do you need two (Alvira and MWB) to organize and run when the best one will do the job with more extras than the other two offer put together, EMSISOFT, and super-quck support, sport!