Keeping your personal data safe doesn’t have to be difficult, as long as you keep sensitive information encrypted and under your control. That’s why this week we’re looking at the five best file encryption tools you can use to encrypt your data locally.
Title photo by andrey_l (Shutterstock)
For the purposes of this roundup, we’re focusing on desktop file encryption tools – the ones you use on your own computer to encrypt your own private data. We’re not examining cloud services that promise to encrypt your data, or business services that say they offer encryption. The goal here is to find the best tools you can use to lock down your sensitive files — whether they’re photos, financial documents, personal backups, or anything else — and keep them locked down so only you have the key. For those unfamiliar with the topic, we have a great guide on how encryption works, and how you can use it to keep your own data safe.
With that out of the way, here are your top five, in no particular order:
VeraCrypt (Windows/Mac/Linux)
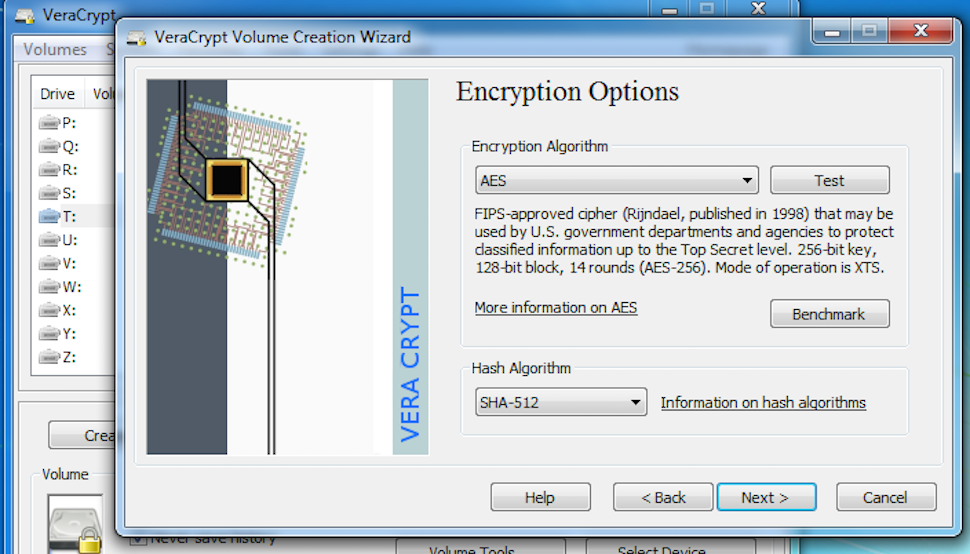
VeraCrypt is a fork of and a successor to TrueCrypt, which ceased development last year (more on it later.) The development team claims they have addressed some of the issues that were raised during TrueCrypt’s initial security audit, while largely maintaining its familiar interface. Like the original, it’s free, with versions available for Windows, Mac and Linux.
VeraCrypt supports AES (the most commonly used choice), TwoFish and Serpent encryption ciphers, and allows the creation of hidden, encrypted volumes within other volumes. Its code is available to review, although it’s not strictly open source (because so much of its codebase came from TrueCrypt.) The tool is also under constant development, with regular security updates and an independent audit in the planning stages (according to the developers.)
AxCrypt (Windows)
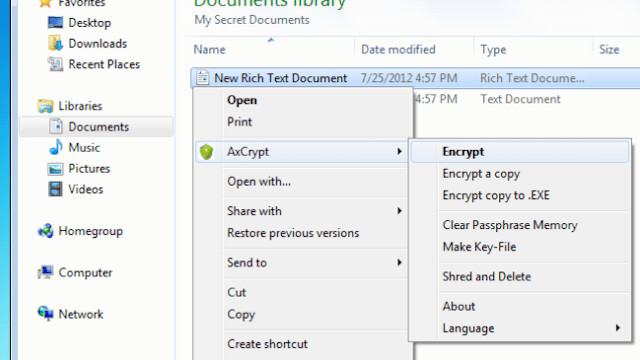
AxCrypt is a free, open source, GNU GPL-licensed encryption tool for Windows that prides itself on being simple, efficient and easy to use. It integrates nicely with the Windows shell, so you can right-click a file to encrypt it, or configure “timed,” executable encryptions, so the file is locked down for a specific period of time and will self-decrypt later, or when its intended recipient gets it. Files with AxCrypt can be decrypted on demand or kept decrypted while they’re in use, and then automatically re-encrypted when they’re modified or closed.
It’s fast, too, and allows you to select an entire folder or just a large group of files and encrypt them all with a single click. It’s entirely a file encryption tool however, meaning creating encrypted volumes or drives is beyond its capabilities. It supports 128-bit AES encryption only, offers protection against brute force cracking attempts, and is exceptionally lightweight (less than 1MB.) It also has a lot of command line options, so you can fire up the command prompt in Windows and perform more complex action sequences.
BitLocker (Windows)
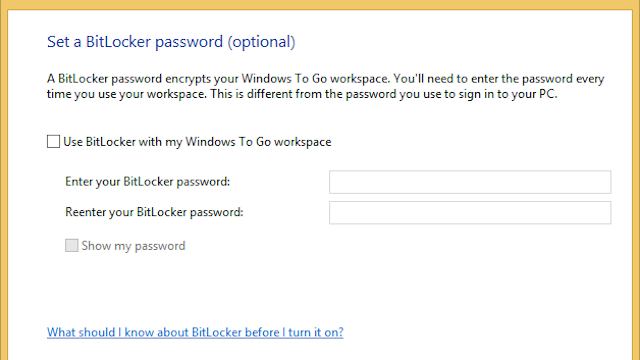
BitLocker is a full-disk encryption tool built into Windows Vista and Windows 7 (Ultimate and Enterprise), and into Windows 8 (Pro and Enterprise), as well as Windows Server (2008 and later). It supports AES (128 and 256-bit) encryption, and while it’s primarily used for whole-disk encryption, it also enables encrypting other volumes or a virtual drive that can be opened and accessed like any other drive on your computer.
It supports multiple authentication mechanisms, including traditional password and PINs, a USB “key,” and the more controversial Trusted Platform Module (TPM) technology, which uses hardware to integrate keys into devices. BitLocker’s integration with Windows makes it accessible to many people, and a viable disk encryption tool for individuals looking to protect their data. One concern? Since the code is locked into Windows, you can’t review it, and it’s sometimes asserted that government agencies have backdoor access to decrypt data (though Microsoft denies this).
GNU Privacy Guard (Windows/Mac/Linux)
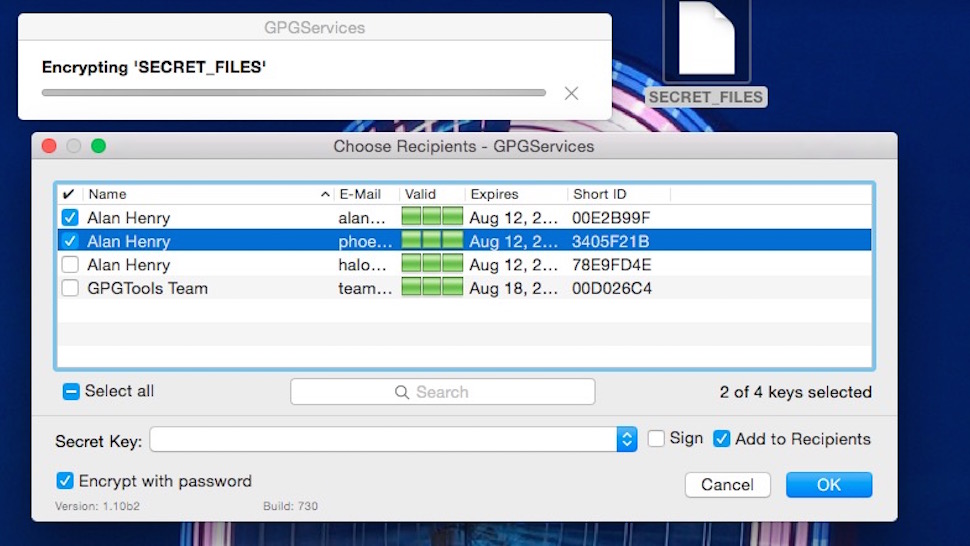
GNU Privacy Guard (GnuPG) is actually an open-source implementation of Pretty Good Privacy (PGP). While you can install the command line version on some operating systems, most people choose from the dozens of frontends and graphical interfaces for it, including the official releases that can encrypt everything from email to ordinary files to entire volumes. All GnuPG tools support multiple encryption types and ciphers, and generally are capable of encrypting individual files one at a time, disk images and volumes, or external drives and connected media.
The key is finding a front-end or a client that does what you need it to do and works well with your workflow. The screenshot above was taken using GPGTools, an all-in-one GnuPG solution that offers keychain management as well as file, email, and disk encryption for Mac.
7-Zip (Windows/Mac/Linux)
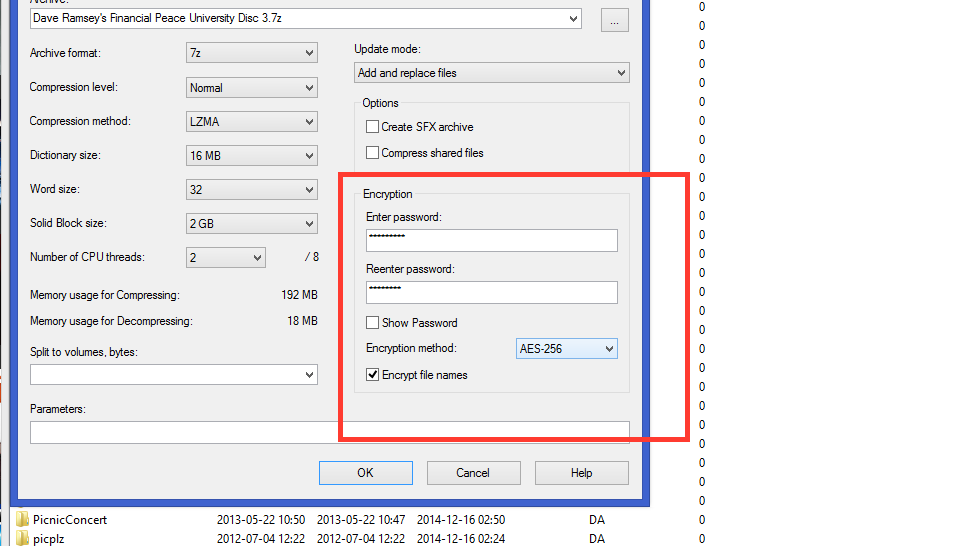
7-Zip is actually a lightweight file archiver — and our favourite archive utility for Windows. As well as being amazing at compressing and organising files for easy storage or sending over the internet, it’s also a strong file encryption tool, and is capable of turning individual files or entire volumes into encrypted volumes. It’s completely free, even for commercial use, and supports 256-bit AES encryption. While the official download is Windows only, there are unofficial builds for Linux and Mac systems as well. Most of 7-Zip’s code is GNU LGPL licensed and open to review.
Compressed and encrypted archives are easily portable and secure, and can be encrypted with passwords and turned into executables that will self-decrypt when they reach their intended recipient. 7-Zip also integrates with the shell of the operating system you’re using, making it usually a click away from use. It’s also a powerful command line utility.
Honourable Mentions
We have two honourable mentions this week. First is Disk Utility (Mac), which is bundled with OS X as a disk repair and management tool. Disk Utility can also encrypt drives and volumes, and since Mac OS X can create a compressed volume just by right-clicking a file, series of files, or a folder and selecting “Compress”, Disk Utility makes encrypting anything you want extremely easy.
Second, we should tip our hats to the venerable old TrueCrypt, our previous champion. We covered the meltdown of TrueCrypt when it happened, with the developers abruptly abandoning the project, claiming that it’s no longer secure, in the middle of their independent security audit. The developers suggested switching to BitLocker, and pushed out a new version that’s widely considered compromised. However, the older version, 7.1a, is still widely regarded as safe, even though development on it has been abandoned, and the tool has been left without security updates since then. Many people stand by it even though it’s a dead project, others have built their own projects on top of it (see VeraCrypt, mentioned earlier), and others keep using the last safe version.
Have something to say about one of the contenders? Want to make the case for your personal favourite, even if it wasn’t included in the list? Tell us what you use (and why) in the comments.
Comments
One response to “Five Best File Encryption Tools”
I think this should have been broken up into two groups: the disk encryption/encrypted virtual partition ones (VeraCrypt and Bitlocker) and the per-file-encryption (GPG and AxCrypt, and I guess 7-Zip although it is a weird case too).
Both types are very valuable, but they fit very different use cases.
I too see problems with this article, with the way it compares apples and oranges. Splitting these applications into two groups still does not go far enough. Generally there are three categories: full disk encryption (FDE), volume encryption, and file encryption. FDE is a control against a different threat than the other two categories. Then there’s symmetric vs asymmetric, again, different use cases like you have commented. An article suggesting the best apps for each use case would be more useful.
Thanks for this great encryption tools