2FA
-

Update Your Snapchat Password Immediately
Snapchat users have bombarded with repeated, unexpected two-factor authentication (2FA) text messages this week, but it’s unclear whether the cause is due to a glitch on Snapchat’s end, or due to hackers attempting to break into unsecured Snapchat accounts en masse. Either way, it’s not a bad idea to update your Snapchat password right away.
-
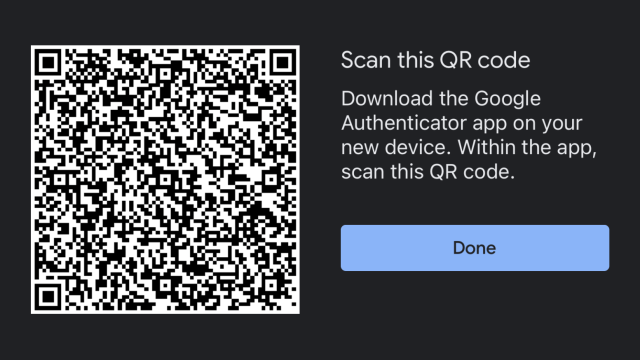
How to Move Google Authenticator to a New iPhone
Finally, Google has updated its useful Authenticator app on iOS to allow users to export their myriad of tokens and import them on another iPhone directly within the app. This has been my biggest hitch about using Google Authenticator, as it meant that you were in for a world of annoyance when upgrading or switching…
-
Get Your Nest Devices Ready For Mandatory Two-Factor Authentication
Google is about to turn on two-factor authentication (2FA) for all Nest users. That’s a good thing! Most people shouldn’t experience any difficulties with this security-enhancing measure, but there are a few quirks you should know about.
-
Microsoft Kills Password Expiration Rules In Latest Version Of Windows 10
Microsoft has made a move with the most recent version of Windows 10, the May 2019 update. Among the changes introduced, Microsoft has removed the need to change passwords every 60 days. With emerging technology such as 2FA and better breach detection, Microsoft is trying to cut the bungee to password rules developed decades ago…


