Before you share the private contents of a Zoom meeting publicly — ideally for noble reasons — know that there are lots of different ways that the meeting’s host can pinpoint you as the leaker. And that could come with a whole host of legal or professional problems.
I was a bit shocked to find just how easy it is to figure out which of a meeting’s participants is responsible for leaking the meeting. While I’ve pored over the contents of my Zoom Pro account’s settings, I never stumbled across Zoom’s watermarking features — mainly because they’re reserved for admins of fancier enterprise accounts. But they’re quite powerful, and they’re not something I’d expect most people to know about. (Hat-tip to The Intercept for pointing these methods out.)
A company can watermark its Zoom meetings in two different ways. First, there’s the obvious one: video watermarks. If a company enables this feature, then part of a user’s email address will be superimposed on the video when they’re watching a shared screen; similarly, the person sharing their screen will have part of their email address stuck onto the video, like so:
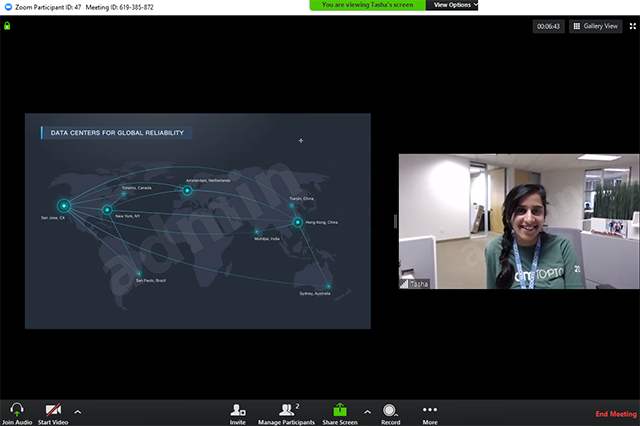
If a company is using this watermarking feature, it’ll be obvious — I don’t believe you’ll see any kind of warning icon. All you’ll need to look for is the hard-to-see text over your face during screen sharing. That text does not appear on a webcam feed during a regular video chat (if I’m reading Zoom’s guide correctly).
The second method is the more insidious one, which I suspect nervous companies will use more than the first. It’s audio watermarking, and it’ll be completely imperceptible to most people unless they know what to look for — a tiny green icon to the right of the green padlock icon in your Zoom meeting, which indicates the feature is active.
The good news (for leakers) is that a recording needs to be around two minutes in length, at minimum, to ensure that an audio watermark will appear in any official recordings of the meeting. Less than that, and you’re rolling the dice. Your audio might have a watermark; you might get away without one.
The bad news is that whatever Zoom injects into the audio to identify someone isn’t something you’d be able to hear. The way Zoom does its audio watermarking is something that Zoom itself analyses for companies upon request — there isn’t a magical software tool a company can use to extract the watermark from leaked audio, nor can you ever be sure that you’ve obfuscated a meeting’s audio enough to mess up any hidden watermarks. There are just too many potential avenues.
[referenced id=”1036991″ url=”https://www.lifehacker.com.au/2020/11/how-to-stop-a-zoombombing/” thumb=”https://www.gizmodo.com.au/wp-content/uploads/sites/4/2020/11/19/lgu2g1vh8pizscextvrz-300×169.jpg” title=”How to Stop a Zoombombing” excerpt=”The dreaded “Zoombombing” is a risk for all Zoom meetings, even private rooms secured with a passcode and data encryption. All it takes is for the invite to wind up in the wrong hands, and suddenly you have someone screaming randomly in your work meeting — or worse.”]
So, if you’re required to log into an official Zoom account to attend a meeting, and you see either watermarking tool enabled, think twice about recording and sharing its contents — even if you’re doing it for a justified, moral, or legally appropriate reason. What you share might get traced back to you, even if you think you were covering your bases in a clever way.
And these are just Zoom’s watermarking tools. There are plenty of other ways for companies to track down Zoom leakers, including: looking at the devices used to connect to the meeting and comparing that to screenshots or videos taken from the meeting; inspecting the participants in a shared Zoom call to see who might have shared based on the position they appear on the screen; and inadvertently sharing some portion of your desktop or other identifying characteristics (like a pop-up notification with your email address). The Intercept has a pretty comprehensive list of ways would-be leakers can screw this up. It’s worth a read.
Leave a Reply
You must be logged in to post a comment.