Last week, the internet erupted in anger after discovering Lenovo has been bundling Superfish, a horribly insecure piece of adware, on new machines. Superfish isn’t the only program of its type out there, though. Here are a few others you should check your PC for.
Our friends at How-To Geek remind us that there are lots of other programs out there that inject ads into your browser — and, in doing so, break the security of HTTPS, just like Superfish. They may not come pre-installed on machines like Superfish did, but you can still get them from downloading otherwise “legit” software — even from a “legit” site like CNET’s Download.com.
So, while you’re cleaning up from the Superfish debacle, you should also check for the following pieces of malware. Follow our instructions for removing Superfish, but look for these programs in steps 3 and 6:
- Sendori
- Purelead
- Rocket Tab
- Super Fish
- Lookthisup
- Pando
- Wajam
- WajaNEnhance
- DO_NOT_TRUSTFiddler_root (Fiddler is a legitimate developer tool but malware has hijacked its cert)
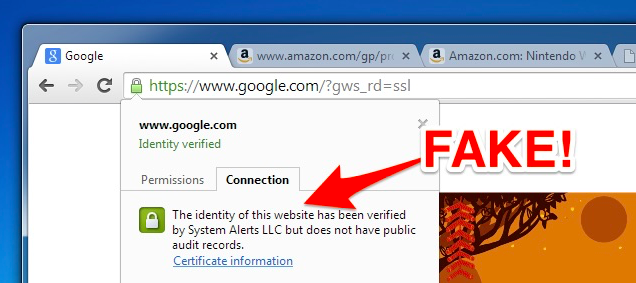
- System Alerts, LLC
- CE_UmbrellaCert
Those aren’t the only ones, either — but they’re some of the most common that How-To Geek found. Comodo is also apparently bundling an HTTPS-breaking program called PrivDog with its Comodo Browser, and Lavasoft is including similar malware with its Ad-Aware program, according to Ars Technica.
If you see any of these installed on your computer or in your Trusted Root Certification Authorities folder, delete them, and uninstall their corresponding programs. How-To Geek says you should also clear the certificate caches in your browser after doing so. You can see the full instructions for doing so, along with an explainer on how these programs work, at the link below.
Download.com and Others Bundle Superfish-Style HTTPS Breaking Adware [How-To Geek]
Comments
3 responses to “The Other Superfish-Like Malware You Should Check Your PC For”
IF you get a laptop, rebuild it from the ground up. It gets rid of all the bloat you might miss.
That sounds like it is easier said than done?
Got a lenovo computer. Download the SCCM driver pack. Put in Windows disk. Remove all partitions and install.
Put driver pack on from USB or whatever. Do through device manager and point every device at the location of the driver pack.