Whether your files are stored on Dropbox, iCloud or Mega, they could do with a little more security. It’s impossible to make them “hack proof”, but there are a few steps you can take to make your data as secure as possible — and still convenient to access. Let’s walk through those steps.
Title photo made using Slavoljub Pantelic (Shutterstock) and kzww (Shutterstock). Additional photos by Lulu Hoeller, Jeremy Keith, tubedogg, Ryan Somma, and See-Ming Lee.
There’s no such thing as perfect security, but that’s no excuse to do nothing, especially when boosting your security is easy. Don’t fall for the trope that “if you want it secure you shouldn’t store it in the cloud”, Cloud storage is a convenient, accessible technology that gives us access to our data anywhere, on multiple devices. It helps us work and makes our lives easier. It’s silly to not use useful technologies simply because of the risk that something bad might happen. Let’s talk about how you can mitigate that risk.
Step One: Check Your Password And Enable Two-Factor Authentication (If Available)
Let’s start with the basics. First, check the passwords you use for your cloud accounts. Are you using the same ones for multiple services? Are you relying on memory or some other clever tricks to help you keep track of them? Stop now, get a password manager (yes, they’re more secure even if they seem like a single point of failure), and set different passwords for each service.
Next, enable two-factor authentication for all of them if you can. Two-factor authentication isn’t foolproof, but it’s the next most important step to securing your accounts — and by proxy, your data. While you’re in your password settings, take a look at your security questions, and how the service handles password resets. Make sure you’ll be notified if someone tries to reset your password, and if there are security questions involved, make sure you choose obscure questions. Lie or give creative answers to those questions that only you know. You don’t want someone getting into your storage the way intruders got into celebrity iCloud accounts earlier this year.
Step Two: Audit Your Connected Apps, Devices And Services

Your next step is to take a look at any connected apps and devices with access to your cloud storage. In Dropbox, for example, you can see all of them in your account security settings. (Alternatively, log in to your Dropbox account, click your name and select “Settings”, then click the “Security” tab.) Similarly, at Box, you can click here to go to your settings, log in, then click the “security” tab to enable two-factor authentication and review your connected apps. If there are any applications listed that you no longer use or don’t recognise, remove them.
You don’t want some old app to be compromised and subsequently lead someone to get access to your account. This happens more frequently on social networks like Facebook and Twitter, but keeping those lists clean is a good habit to get into. All it takes is for someone to use read/write access through some ancient-but-popular app to get easy backdoor access to lots of user accounts.
While you’re at it, make sure any old devices you use are cleaned out as well. Take special care with this step though — if there are files on those devices you want to keep, they will be immediately unlinked and stop syncing, and the next time the device calls home, your local copies of synced files may be deleted.
Step Three: Check Your Provider’s Stance On Privacy And Encryption
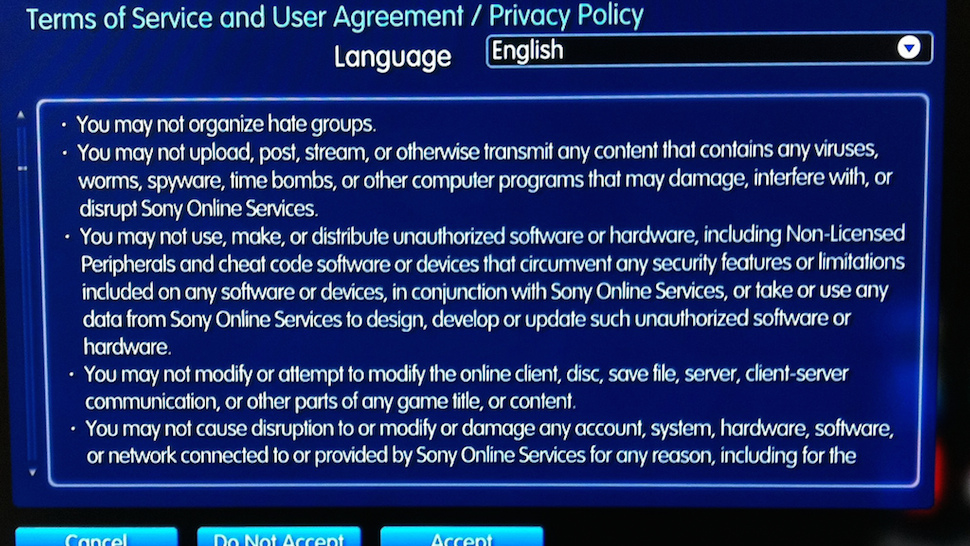
Next, do a little digging to see how your cloud storage service handles privacy, and how committed it is to protecting your data. We touched on this a while ago for some of the most popular services, but not all of them. Check what access your provider gives itself to your data. Review the security it claims to offer as well. Some companies encrypt your data at rest on their servers, and note that even they have no idea what you’re storing with them. Others reserve the right to access your data whenever they choose, and use vague, hand-wavy terms like “bank-level security” when they talk about encryption. Those are all bad signs, and generally mean that they either don’t take security seriously, or don’t think you’re smart enough to.
Take some time and review the terms of service agreements, security and privacy policies of the services you’re trusting with your data. In some cases, you’ll see that your trust is well-placed, but if anything gives you pause, the least you can do is ask customer support what a given clause in the agreement means, or Google it to see what other people are saying. If you’re worried about those policies and terms changing — and they often do — previously mentioned Paranoid Paul can keep track of them for you and notify you when they change.
Whether you opt to move on from a service with less-than-stellar security or an intrusive privacy policy is up to you. However, it’s worth noting if a service gives itself access to your data freely and doesn’t take security seriously enough to explain how it protects your data, it probably won’t respond well if someone attacks it — and may not have anything in place internally to stop an intruder from getting to your information. You can do better.
Step Four: Audit Your Files And Remove Or Encrypt Sensitive Data

Many of us use cloud storage for just about everything. Part of getting so much free storage is that you don’t really have to think about what you upload — you can just upload it. That’s great unless you’re thinking about what may be lost if someone gets access to your accounts. Take some time and go over what you store in each cloud storage account and identify it by risk. Think about how bad it would be to lose that information, and whether you have it backed up anywhere. If the service is one of those (like iCloud or OneDrive for example) where the company can access your data at any time, consider whether your data may violate their terms of use, even slightly.
It doesn’t take much for an overzealous company to shutter your account. Back in 2011, a German photographer had his account closed suddenly because Microsoft decided his professional work was “questionable”. Another OneDrive user lost his entire Microsoft account over some files stored in a private folder, accessible only to him.
If there’s anything you’d hate to lose, or anything you’re worried an overzealous algorithm may close your account over, it’s time to either remove it from the cloud and store it locally, or encrypt it. We’ve given you a primer on encryption in the past, and this method of compressed encryption using 7-Zip in Windows (Mac users should try Keka for a free alternative) will get the job done quickly and easily. Encrypting those files and archives with a password may make it more of a hassle to access on other devices, especially on your smartphone or tablet, but it’s a huge security boost, especially if you use your cloud service for things like financial documents or contract.
Step Five: Consider Diversifying with Privacy- And Security-Conscious Services
With so much free cloud storage floating around from services happy to give it away just for signing up, it makes sense to spread out your critical data to different services so if one of them gets hacked, loses your data, or something else happens, you’re not at a complete loss. Doing this accomplishes two major things: First, it makes sure that losing one cloud storage service isn’t the end of the world when it comes to you actually being able to function. Second, it protects you from losing everything if someone breaks into your account via social engineering, as opposed to password trickery or exploits. Of course, keeping sensitive data encrypted will make sure that person doesn’t get away with much, but keeping your data diversified means that the odds of an intruder finding something useful are slimmer than if you used one big bucket for everything.
Similarly, regardless of what service you prefer, consider relying on cloud services with serious encryption and security features for your most sensitive data. There are plenty of services that do it well, like Spideroak and Tresorit. Both are worth a look if you know you’ll need to store, share and access sensitive information on multiple devices.
Reminder: Cloud Storage Isn’t Backup
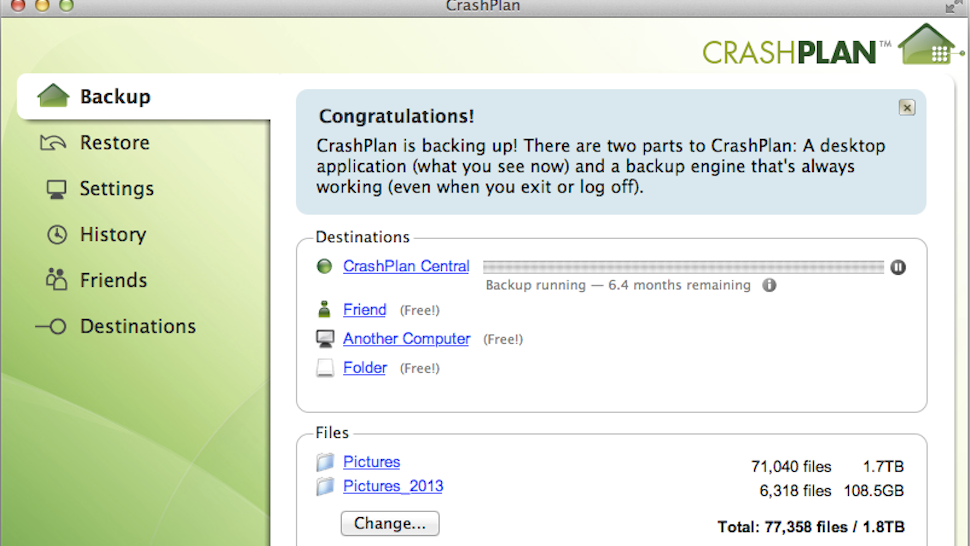
Finally, a quick reminder: cloud storage is not backup. Or more precisely, sync is not backup. If your data is removed for any reason from the cloud end, sync means it’s removed from your local machine as well. As well, most cloud services don’t offer fine revision histories for the files you sync, a feature that’s critical to a good backup service.
This is where we point out that cloud storage and sync is not the same as online backup. You should trust the latter to keep your data safe, but not the former. It’s important to keep more than one backup of your data, including one that’s offsite. Using an online backup service means that your data is kept regularly updated, complete with granular revisions, stored and encrypted in someone else’s data centre, where it’s regularly updated as well. Of course, keep your data backed up locally as well. There’s nothing wrong with storing backups on an external hard drive or a NAS, especially for quick restores if your system dies. However, that NAS and hard drive is worthless if your house burns down or someone breaks in and cleans you out. When it comes to online backup, we prefer Crashplan because it’s easy to set up and offer strong encryption, but you have plenty of options.
Some of these steps are things we’ve mentioned before on their own, but if you work through them one at a time, you can have a huge impact on your data security in a short period of time. It doesn’t take a lot of effort to significantly improve your security. Does this make you “hack-proof?” Of course not: but it certainly makes you a more difficult target — one not be worth the effort required to get your data — and that’s a very worthwhile improvement.

Comments