“Another day, another migraine” is a wonderful morning mantra from Spongebob’s Squidward Q. Tentacles, which you can also apply to your account security on a near-weekly basis. It feels as though there is always some new data breach or unfortunate leak you have to deal with, and this week’s exercise is the big one.
The biggest one, actually: 1,160,253,228 combinations of emails and passwords, affecting 773 million unique email addresses in total.
To put that in perspective, security researcher Troy Hunt calls this “the single largest breach ever to be loaded” into his helpful website Have I Been Pwned.
And odds are good that you have, indeed, been pwned. Perhaps even pwned a few times, depending on how many times your various accounts appear in this huge “Collection #1” data breach — a big combination of a lot of other data breaches going as far back as 2008 (potentially).
Are you affected?
Probably. But just to be sure, head on over to Have I Been Pwned and type in the email address you use (or have used) for various services around the web. As the results will show you, you’ve probably been the victim of quite a few data breaches. If you’re today’s lucky winner, you’ll now count “Collection #1″ among them.
Which passwords should you worry about?
If you’ve been poking around Have I Been Pwned, you’ve probably noticed that there isn’t any way to get a definitive list of which account/password combinations appear in the various hacks and breaches. Obviously, providing such a list would be a security issue in itself, since anyone could then use the site to find new account credentials to try out.
Instead, Hunt has crafted up a separate password-scanning tool. Input a password you use (or used to use), and you’ll be able to see if it appears on any of the data breaches in the website’s large repository.
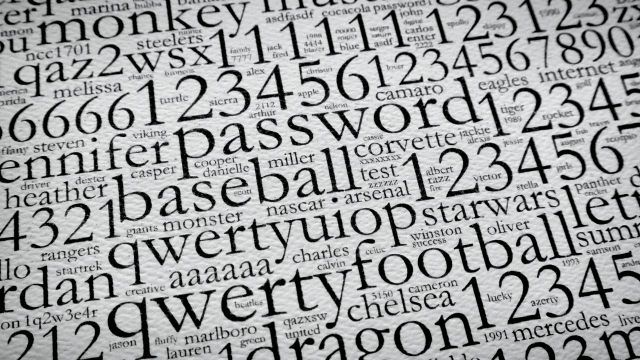
This won’t do you much good if you (foolishly) use a generic password, such as “hunter2″ or “password12345”. But if your password is pretty strong and likely unique, this tool can be a great warning sign that it’s time to change it up — if you’re still using the password, that is.
Now what?
Thankfully, the “Collection #1″ data breach only involves emails and passwords — not addresses, real names, credit card numbers or any other disastrous data points. While you won’t have to go through more annoying processes such as changing your credit card, you’ll still want to take some steps to get a little more control over your (now-exposed) accounts.
First, the obvious: If your passwords show up in Have I Been Pwned’s database, it’s time to change them. If you have a lot of unique passwords for all of your accounts — and you should! — then checking this is going to be a pain in the butt. You might want to investigate a password-management tool such as 1Password, which can do this all for you and let you know whenever your passwords show up in a new breach.
And if you aren’t already using a password-management app, now is a great time to start. There’s no reason why each of your accounts shouldn’t have strong, unique passwords. This keeps you safe by ensuring that these kind of security breaches only affect one of your accounts, rather than the single “secure” password you use for every account.
Also, a tool such as 1Password makes it easy to manage complex passwords (or passphrases). Instead of having to remember the long string of letters, numbers and symbols you’ve created — including capitalisations — whenever you’re logging into something, you just authenticate into 1Password instead and copy/paste a service’s complicated password. It’s as easy as that.
Of course, you can always do more. A strong password is great, but it’s even better when you’ve partnered it up with two-factor authentication. You should be using two-factor authentication for any websites that support the practice, which you can check right here.
Even if someone gets their hands on your amazing password, they won’t be able to do anything with it as long as you still have to approve any new logins — including logins from a location that isn’t where you typically are, for example.
Comments