Spying on someone’s computer is bad. As in “go to jail” bad. However, there are a few very narrow exceptions, like monitoring your kids or employees. If you fall in this category (or just want to know how someone might be monitoring you), here’s how.
First, a big, big disclaimer: monitoring another person’s computer without their permission isn’t just wrong, it can be a crime. There are only a few very specific conditions in which you’re allowed to monitor a computer someone else uses. For example, an employer may be allowed to monitor certain things, but only on hardware the company owns. A parent can track their child’s activity because they’re legally responsible for their children. However, outside this situations, there isn’t much wiggle room, and there probably shouldn’t be.
Even in cases where it may be legal, you could still open yourself up to privacy lawsuits if you’re not careful. You might end up recording an employee’s Facebook password through logging software, but if you then used that to access their private messages, that would cross the line.
Finally, tracking someone else without their knowledge (even if it’s legally OK to do so) will almost certainly violate their trust. If you’re a parent with a teenager, monitoring their web activity may be acceptable, but you could alienate them. Legal and ethical justifications don’t fix broken trust. Consider the social costs to tracking as well before you proceed.
First, Determine What (and Whether) You Want to Track
Finding out what someone else is doing isn’t as simple as saying “Computer! Watch them and report back to me!” You need to actually know what you’re looking for. If you’re a parent, you might want to give your child privacy, while making sure they’re not visiting seedier parts of the internet. If you’re an employer who needs to monitor an employee to watch for wrongdoing, you might want to log everything. Generally, monitoring falls into three categories:
- Watch for certain activity. This is ideal when you generally don’t care what someone does using a device, as long as they follow the rules. For example, you may want to see when an employee uses Facebook, or a child views porn. Sometimes this can be accomplished with filtering, rather than surveillance, so try to consider all options.
- Monitor all activity in certain apps. Employers may want to monitor certain apps, but don’t want to snoop on their Facebook. You might only care about what they do with company email, chat apps, or proprietary software. In that case, more selective monitoring may be better.
- Monitor all activity in every app. In this case, you may want to see everything someone is doing. This might include monitoring a child’s chat logs if you’re worried they may be into something shady, or keeping tabs on an employee you think may be stealing from the company.
It’s important to decide very specifically what you want to track, because tracking too much can cause legal problems. If you only need to keep employees off of certain websites, don’t use a keylogger. If you want to keep children away from porn, you probably don’t need to monitor every Facebook message. Keep your tracking minimal to avoid any complications down the road.
Choose the Right Software
Once you’ve decided how and why you want to monitor someone’s computer, you need to get the right software. While there are a ton of monitoring tools out there, we have a few suggestions from reputable organisation. Keep in mind, you’re dealing with surveillance software. You may be able to find a free keylogger from a random developer’s website, but you can’t always know if that tool will be secretly phoning home. In this case, it’s best to stick with established companies you know you can trust.
Monitor a Child’s Activity: Parental Control Tools (Windows/OS X)
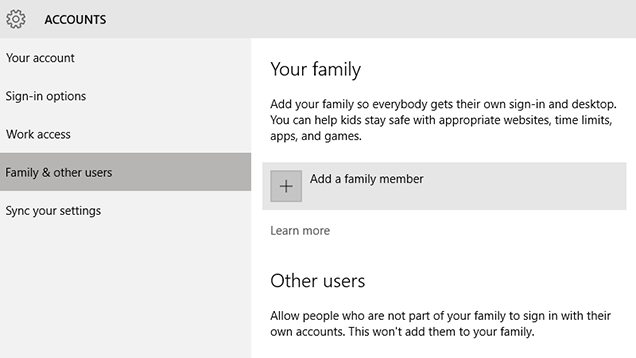
Both Windows and OS X have built-in tools that allow adults to keep tabs on a child’s activity. You can use these to monitor and filter your child’s activity. There are a couple of key differences, but some features are shared between both platforms. Here’s how the features break down:
- Block or monitor website and app usage (Both)
- Set time limits for computer usage (Both)
- Filter apps and games by age restriction (Both)
- Hide profanity in dictionaries (OS X)
- Block certain hardware, like cameras (OS X)
- Block communication with certain people via select apps like messaging and email (OS X)
To use these features, both platforms require you to set up a child’s account. You can find information on how to create a new child’s account on OS X here or on Windows 10 here. You can also find information at these links on how to manage each platform’s settings.
Keep Track of An Employee’s Productivity: ActivTrak (Windows/OS X)
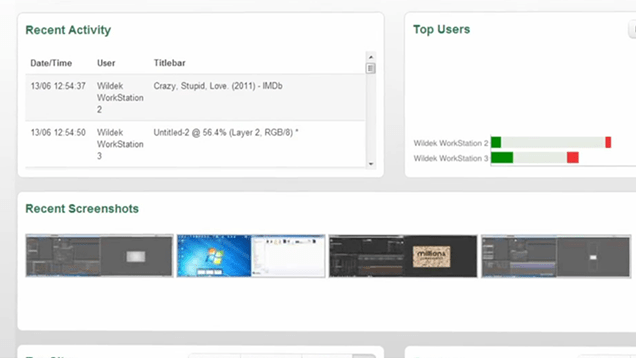
If you’re an employer who wants to get a more detailed look at what your employees are doing, ActivTrak is a decent solution. It allows you to monitor several employees computers at once and provides detailed reports on a user’s activity. Here are some of the key features:
- Records statistics on when and how often applications are used.
- Take periodic screenshots of user activity.
- Generates charts visualising time spent in various applications.
- Sends alert messages when a user begins specific, unwanted activity.
- Can be installed remotely if company uses ActiveDirectory (paid version only).
As an admin, you can log into a web-based control panel to view activity usage stats within minutes after setting up the computers in your office. You can set custom categories based on what’s productive and unproductive in your office. For example, your social media intern using Facebook may be “productive,” but a case manager might not be. You can also use the Reports tab to see which applications and websites are most common among one or all of your employees.
The free tier of this service allows you to monitor three users (called “agents”) with one admin and a limited amount of storage. You can pay to add more agents or new features, like the remote installer. The paid tiers begin at $US336/year for 5 agents and go as high as $US1920/year for 50 agents. Obviously, the higher tiers aren’t something you’re going to want unless you know that your business is going to need it.
Investigate An Employee For Potential Wrongdoing: Spector
If you have a serious suspicion that an employee might be doing something illegal or against company policy, SpectorSoft has a huge suite of software you can use for both short-term and long-term investigations. The basic Spector CNE Investigator is designed for short-term investigations and comes with a host of tools:
- Takes screenshots every 30 seconds.
- Trigger screenshots after keywords are used or specific applications are opened.
- Track website usage, time spent on sites, and time of last visit.
- Store and archive corporate email.
- Record instant message chat logs from virtually all messaging platforms.
- Tracks name, file type, and time of documents downloaded or uploaded to the computer.
- Records all keystroke activity on the user’s machine. Optionally, you can choose not to record passwords.
SpectorSoft also offers Spector 360 which includes advanced reports to analyse a user’s activity, global keyword search to find specific suspicious words or phrases among all platforms, and web filtering. The company says that Spector 360 is designed for more long-term investigations and monitoring, so most employers will probably be ok with CNE Investigator.
All SpectorSoft programs are paid apps, and you can only get a price by calling in for a quote. Naturally, this means it’s probably pretty expensive and this isn’t the kind of thing your average person will want. However, if you’re running one of those major studios that keeps leaking trailers, this might be something you’re interested in.
Depending on your needs, you may need other monitoring software and there’s plenty more out there. These are our suggestions for a few common types of monitoring. Keep in mind, in virtually all cases, you’ll need physical access to the computer where you want to set any of this software up.
Lifehacker’s Evil Week highlights the dark side of life hacking. How you use that knowledge is up to you.
Comments